Difference between revisions of "Zimbra Two-Factor Authentication"
(Created page with "All XMission Zimbra email accounts support a beneficial security practice known as '''two-factor authentication''' (aka, 2FA). Two-factor authentication provides mailbox prote...") |
|||
| Line 11: | Line 11: | ||
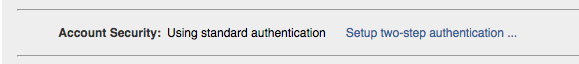
Two-factor authentication is included by default for all XMission Zimbra accounts. Two-factor has to be enabled from the Zimbra webmail interface for all accounts. The setting is found in under Preferences > Accounts > Account Security, Setup two-step authentication | Two-factor authentication is included by default for all XMission Zimbra accounts. Two-factor has to be enabled from the Zimbra webmail interface for all accounts. The setting is found in under Preferences > Accounts > Account Security, Setup two-step authentication | ||
| − | + | [[file:2fa_XM_Zimbra_AccountSecurity.png]] | |
Simply click the "Setup two-step authentication ..." link to begin the configuration process. | Simply click the "Setup two-step authentication ..." link to begin the configuration process. | ||
| Line 17: | Line 17: | ||
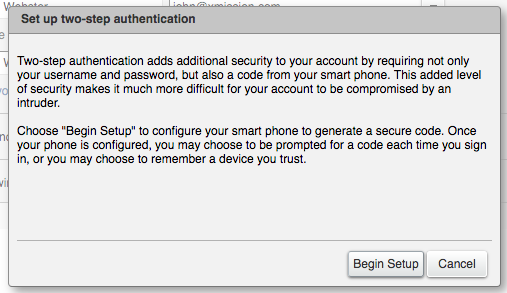
The first step shows a brief description about two-step authentication. Next click on Begin Setup. | The first step shows a brief description about two-step authentication. Next click on Begin Setup. | ||
| − | + | [[File:2fa_XM_Zimbra_Begin_Setup.png]] | |
Next step asks for your current password ("what you know"). Enter and click on Next. | Next step asks for your current password ("what you know"). Enter and click on Next. | ||
| − | |||
| − | |||
The next step establishes the second component the user must have, (the "what you have" such as a smartphone application or usb key). The Two Factor authentication wizard will show a Wiki link with the OTP Apps Zimbra recommends. In this example we will be authenticating with your smartphone. ([https://xmission.com/blog/2017/02/08/6-steps-to-zimbra-two-factor-authentication-with-yubikey Reference this blog post on 2FA with a USB key].) | The next step establishes the second component the user must have, (the "what you have" such as a smartphone application or usb key). The Two Factor authentication wizard will show a Wiki link with the OTP Apps Zimbra recommends. In this example we will be authenticating with your smartphone. ([https://xmission.com/blog/2017/02/08/6-steps-to-zimbra-two-factor-authentication-with-yubikey Reference this blog post on 2FA with a USB key].) | ||
| − | |||
| − | |||
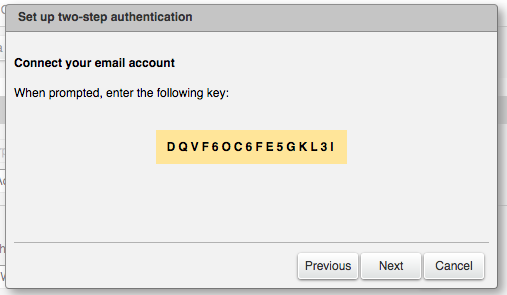
Once you have installed the smartphone app, the Zimbra 2FA wizard will show a unique key that the you must enter in the Smartphone OTP App. | Once you have installed the smartphone app, the Zimbra 2FA wizard will show a unique key that the you must enter in the Smartphone OTP App. | ||
| − | + | [[File:2fa_XM_Zimbra_code_example.png]] | |
| − | How to Install and Configure an OTP smartphone | + | '''How to Install and Configure an OTP smartphone ap'''p |
In this example, we use Google authenticator, but please visit the Zimbra Wiki where you can find other options. In the App Store or Play Store, search by Google authenticator, then click Install. | In this example, we use Google authenticator, but please visit the Zimbra Wiki where you can find other options. In the App Store or Play Store, search by Google authenticator, then click Install. | ||
| Line 51: | Line 47: | ||
All done! Now the app is configured and will show a 6-digit code that changes after 15 seconds. | All done! Now the app is configured and will show a 6-digit code that changes after 15 seconds. | ||
| − | + | ||
'''Finishing the configuration in the Web Client''' | '''Finishing the configuration in the Web Client''' | ||
| Line 106: | Line 102: | ||
Application passcodes: | Application passcodes: | ||
| − | + | Randomly generated. | |
| − | + | Can be created by giving a label and revoked by their label. | |
| − | + | Changing account password will revoke all application passcodes. | |
How to create an application passcode | How to create an application passcode | ||
| Line 146: | Line 142: | ||
Current behavior: | Current behavior: | ||
| − | + | EWS Apple Mail app complains about connection failure and provides option to enter new password, wherein entering correct application passcode does not work. Only option is to Edit Account and provide new password, which works correctly. | |
| − | + | Thunderbird (IMAP/POP3) prompts for new password after some time (after few minutes or sometimes after restarting client) | |
'''Testing Zimbra Desktop with 2FA''' | '''Testing Zimbra Desktop with 2FA''' | ||
| − | + | Pending | |
'''Testing Zimbra Connector for Outlook with 2FA''' | '''Testing Zimbra Connector for Outlook with 2FA''' | ||
| − | + | Pending | |
Revision as of 12:11, 21 March 2017
All XMission Zimbra email accounts support a beneficial security practice known as two-factor authentication (aka, 2FA). Two-factor authentication provides mailbox protection by combining something you know (your password) and something have (your smartphone or USB-key, etc.)
File:Https://wiki.zimbra.com/images/4/4b/Zcs87-2fa-diagram.png
How it works
In simple terms, two-factor authentication prevents unauthorized users from accessing the system because they are very unlikely to have both variables to access the account such as the password and PIN sent to the mailbox owner's smartphone. If either variable is missing, access is denied.
How to enable
Two-factor authentication is included by default for all XMission Zimbra accounts. Two-factor has to be enabled from the Zimbra webmail interface for all accounts. The setting is found in under Preferences > Accounts > Account Security, Setup two-step authentication
Simply click the "Setup two-step authentication ..." link to begin the configuration process.
The first step shows a brief description about two-step authentication. Next click on Begin Setup.
Next step asks for your current password ("what you know"). Enter and click on Next.
The next step establishes the second component the user must have, (the "what you have" such as a smartphone application or usb key). The Two Factor authentication wizard will show a Wiki link with the OTP Apps Zimbra recommends. In this example we will be authenticating with your smartphone. (Reference this blog post on 2FA with a USB key.)
Once you have installed the smartphone app, the Zimbra 2FA wizard will show a unique key that the you must enter in the Smartphone OTP App.
How to Install and Configure an OTP smartphone app
In this example, we use Google authenticator, but please visit the Zimbra Wiki where you can find other options. In the App Store or Play Store, search by Google authenticator, then click Install.
Zcs87-2fa-010.png
Once the app is installed, open it, and click Begin Setup.
Zcs87-2fa-011.png
The app will ask if you want to configure a Manual entry or Scan a barcode. Zimbra Collaboration 8.7 supports only manual entry for now. However, keep in mind the next Bug where it is being discussed to add the option to support barcodes.
Zcs87-2fa-012.png
To configure the App, the users must add an email address and the unique Key from the Zimbra Web Client.
(need image Zcs87-2fa-013.png)
All done! Now the app is configured and will show a 6-digit code that changes after 15 seconds.
Finishing the configuration in the Web Client
Once the user has the App configured and showing the 6 digit code, the user can enter the Code in the wizard window and click Next.
((need image Zcs87-2fa-007.png )
The two-step authentication feature is now enabled, and the user will be prompted for a code in each new Browser, smartphone, computer, or app where he or she tries to access the account.
(need image Zcs87-2fa-008.png)
In the users’ Preferences > Accounts > Account Security (if the Admin has enabled these options under the COS), the user will see more options like the one-time codes, Trusted devices, and Applications. as
(need image Zcs87-2fa-009.png)
Testing Zimbra Two-factor authentication
We recommend testing from a new web browser session on another computer.
Time to test from another web browser, computer, smartphone, or the Zimbra Desktop application, you should successfully pass the two-factor authentication process.
For example on the Web Client: One-time Codes
(need image ref:Zcs87-2fa-015.png)
With the two-factor authentication enabled, there may be a situation where you don't have the secondary device (phone/usb key). This is where Zimbra allows the use of one-time codes. This feature allows you to generate multiple codes to use in case of emergency. The total number of one-time codes can be configured by XMission. If you need these refreshed let us know.
From the Preferences settings for 2FA you will find "One-time Codes" option, click View to see your available codes. You must keep the codes secure (written somewhere, in another device, etc.). Just be certain it is an absolutely secure area where others won't find it.
(Need image Zcs87-2fa-016.png)
Trusted Devices
Zimbra Web Client and Zimbra Touch Client can be configured as trusted devices during the second challenge stage of two-factor authentication. Once the computer/device is established as trusted you will only need to provide standard credentials, bypassing the two-factor code.
How to trust a computer/device
Once the user enters two-factor code in the login screen the user will have to select the check box Trust this computer and click Verify to trust the current computer/device. User can trust more than one computer/device.
(Need image Trusted Devices 1.jpg)
How to revoke trusted computer/device
You can easily revoke a trusted computer/device in Preferences > Accounts > Trusted Devices found in your Zimbra webmail. Revoke trust for any selected device by clicking "revoke this device" link or get rid of them all by clicking on "revoke all other devices" link.
(Need image Trusted Devices 2.jpg)
Application Passcode
Clients such as IMAP or ActiveSync do not support the UI flow needed for TOTP authentication. For these users need to generate application passcode.
Application passcodes:
Randomly generated. Can be created by giving a label and revoked by their label. Changing account password will revoke all application passcodes.
How to create an application passcode
User can create an application passcode by navigating to Preferences > Accounts > Applications and selecting Add Application Code button. User can enter the application name in the Add Application Code dialog and click Next. Application passcode will get generated and it can be used to sign in to your account.
Application specific passcode.png How to revoke an application passcode
Once the user generates application passcode user can revoke it by navigating to Preferences > Accounts > Applications in Zimbra Web Client. User can revoke this application passcode after selecting the required name in the list.
Application passcode.png Known Issues
Zimbra bugs
Bug 103824 {AUTH} Provide 2FA configuration capability in ZCO
Bug 104144 2fa:ReferenceError: AjxDebug is not defined when zimbraFeatureTwoFactorAuthRequired in multinode rolling upgrade environment
Bug 104648 allow clearing 2FA data from admin console
Bug 105678 Application specific password entry should be purged when 2FA disabled from Admin Console
Notes
Disabling two-factor authentication using Admin console does not clear user's two-factor data. Admin can disable user's two-factor authentication in case user is facing issues with authentication using TOTP/scratch codes. Re-enabling user's two-factor authentication using Admin console after user's problem has got resolved will allow user to use two-factor authentication. In future, Bug 104648 will allow Admin to clear user's two-factor data.
Third party issues
Issue - Mail client issues with application passcode
Scenario: User's zimbra account is configured on EWS Apple Mail and Thunderbird (IMAP/POP3). User enables 2FA using Web client, adds application passcodes for Apple Mail and Thunderbird applications.
Expected behavior: Both clients (Apple Mail) and Thunderbird should prompt for new password, user if enters application passcode, authentication should succeed.
Current behavior:
EWS Apple Mail app complains about connection failure and provides option to enter new password, wherein entering correct application passcode does not work. Only option is to Edit Account and provide new password, which works correctly.
Thunderbird (IMAP/POP3) prompts for new password after some time (after few minutes or sometimes after restarting client)
Testing Zimbra Desktop with 2FA
Pending
Testing Zimbra Connector for Outlook with 2FA
Pending